IoT
| |
Pebble Tracker: A Secure, Battery-Operated, Cellular-IoT Prototyping Platform for Blockchain-Based Applications Designed to write sensor readings to a secure blockchain, Pebble Tracker from IoTeX is a secure, battery-operated, multi-sensor… |
|
All You Need to know about Wi-Fi HaLow and How it can Support the IoT Ecosystem Humans aim high, they plan to turn Mars into a home and desire to bring interconnection between people and people, people and… |

|
Here is How Hearable Devices are Evolving to do Just More than Music Hearables to talk about are playing a vital role in our lives. The hearing industry has benefited from advancements in health… |

|
High Performing RA4M2 Microcontrollers for Low Power Consumption and Enhanced Security in Industrial and IoT Applications With the introduction of 12 new RA4M2 Group microcontrollers, Renesas Electronics Corporation has expanded the low power… |

|
New Digital LoRa Baseband IC to Provide Worldwide LoRaWAN Network Coverage and Capabilities in Vertical Industries and IoT Applications SX1303 from Semtech Corporation is a new generation LoRa baseband processor that provides worldwide LoRaWAN network coverage… |
|
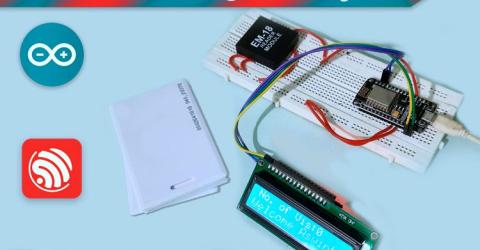
IoT-based Event Management System using RFID and ThingSpeak RFID stands for Radio Frequency Identification, it’s a very simple and inexpensive piece of technology that can be used to make… |
|
How Blockchain can make Internet of Things (IoT) More Secure? This article starts from defining blockchain technology, the difference between blockchain and cryptocurrency, clearing some… |
|
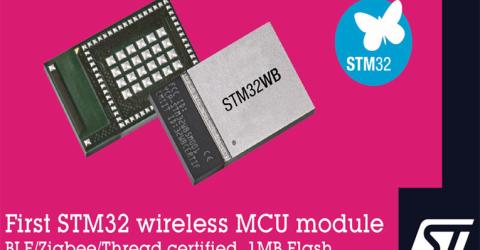
STM32 Based Ultra-Low-Power Wireless Module to Boost IoT Design Productivity STMicroelectronics is offering a solution to accelerate the market of Bluetooth LE and 802.15.4 based IoT devices with a… |

|
How to Configure an ESP Mesh Network using Arduino IDE – Communicate among and between ESP32, ESP8266, and NodeMCU Internet of Things (IoT) has seen exponential growth over the past couple of years. A new study from International Data… |

|
Biometric Access Control: Where We Are Today and What to Expect in the Future Many buildings still use keys, keypads, and access cards to enforce access control. These legacy methods rely on a password or… |

